
Real-time Supply Chain and Vendor Risk Defense
For a holistic real-time assessment of your supply chain
The first solution of its kind for real-time assessment of supply chain risks – with continuous transparency over critical manufacturer or supplier connections. Specifically supports reporting and compliance requirements according to NIS-2, DORA and KRITIS.

A novel approach
The art of anticipating threats.
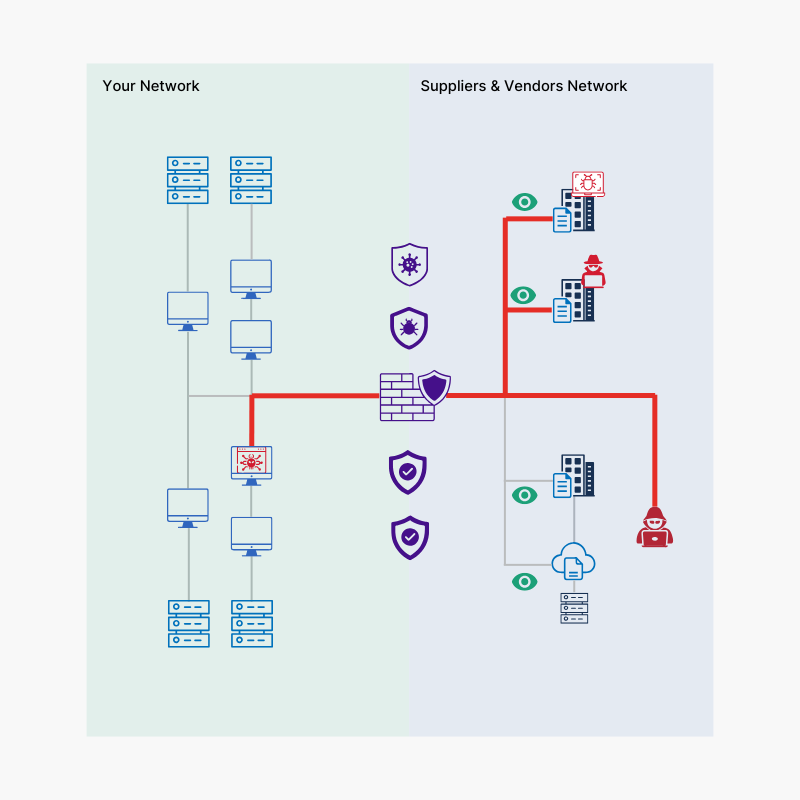
Companies struggle with the reality of fragmented supply chains, non-transparent cloud structures, and minimal insights into the security situation of their third parties. Hidden vulnerabilities remain undetected – until it’s too late.
Cybercriminals specifically exploit these gaps: Suppliers become the easiest entry point into large organizations – often unnoticed.
Our solution closes precisely this critical gap: It actively monitors your supply chain in real-time, detects threats before they reach your systems – and makes hidden risks visible even before they become attack surfaces.
Dynamically integrated threat intelligence flows directly into the risk assessment – so you don’t have to react, but can think ahead.
For companies that don’t like to be surprised.
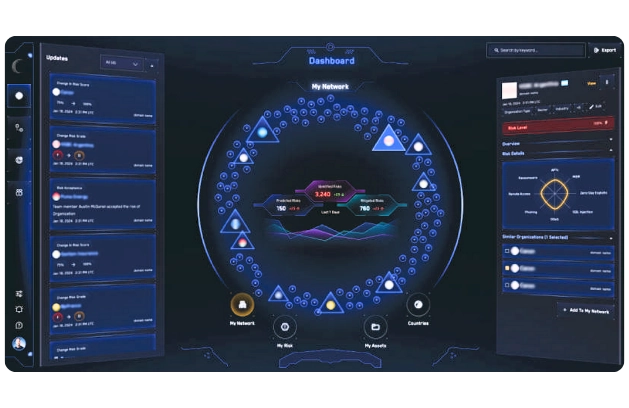
Real risks. Live evaluated.
Benefits at a glance
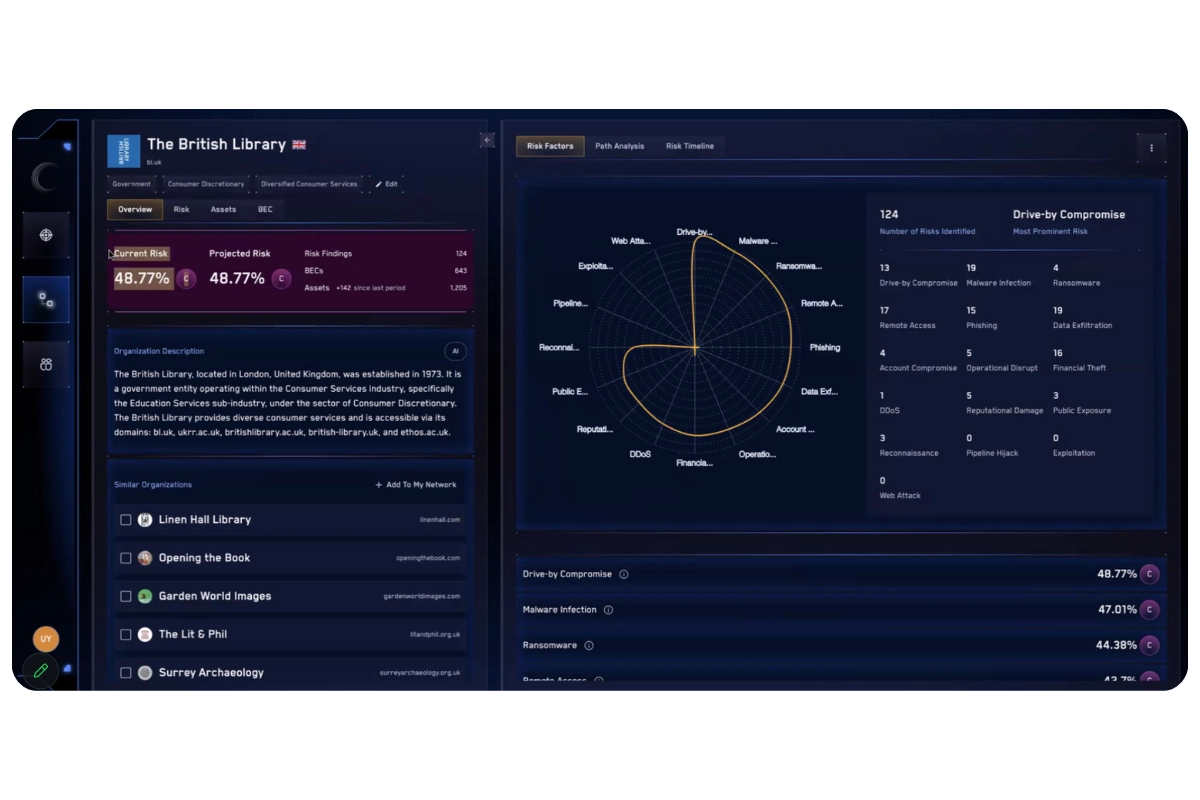
Instead of relying merely on risk values derived from publicly known vulnerabilities, open ports, or leaks, our assessments are based on intelligence-based insights – directly from adversarial sources conducted by our experts with AI-supported signal analyses.
Risk Assessment Based on Real Incidents
The platform identifies the causes of concrete cyber attacks, thereby creating a real advantage – against attackers as well as affected supply chain structures.
Comprehensive Threat Picture
Every known APT group or other relevant attacker activity becomes immediately visible in the system – including real-time assessment of the risk potential, even before an attack occurs.
Transparent Display of Blind Spots and NSB Indicators
Vulnerabilities, hidden attack points, and unrecognized connections in the supply chain are identified – for maximum resilience across all levels.
Traceable and Up-To-Date Risk Values
Risks are presented clearly, comprehensibly, and in a timely manner – including context, cause, and potential impacts.
3A Intelligence: Accurate. Agile. Applicable.
Early Warning System for Impending Attacks
The system provides early indications of threats, even before an actual attack begins – keeping you capable of action before it becomes critical.
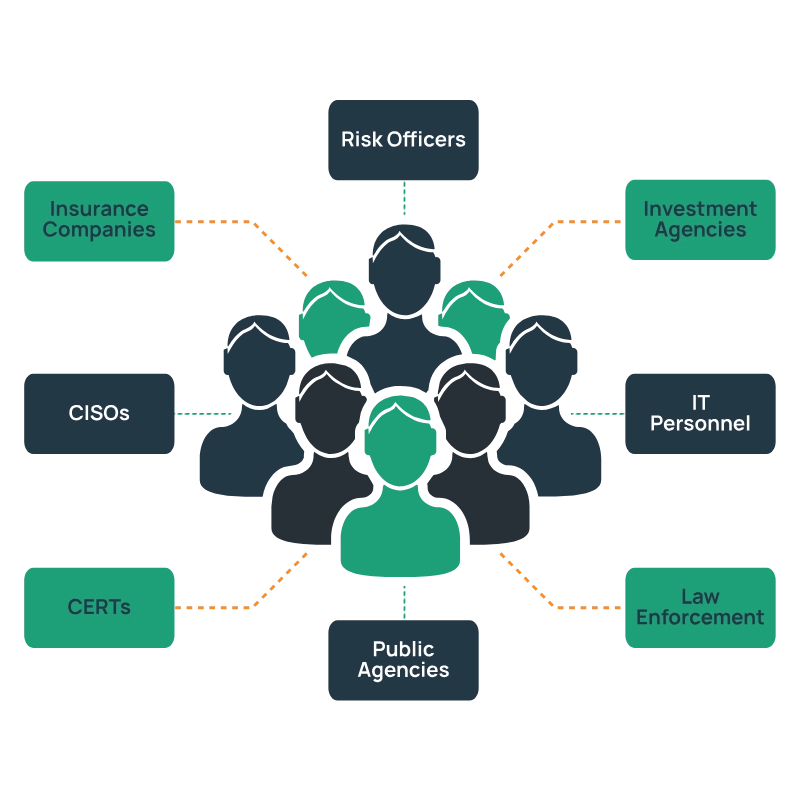
WHO IS IT INTENDED FOR?
Groundbreaking insights.
Determine the risk profile of companies, authorities, NGOs, educational institutions, suppliers – or their customers – with a solution that uses valid, current data.
You no longer have to rely on external information, paper documentation, or audits that are often outdated and inaccurate.
Indicators such as infection rates, malspam campaigns, or ransomware activities provide valuable insights into the cyber risk of your own infrastructure or your third parties – and all this centrally in a single platform.
Unmatched detection of incidents
Achieve true resilience and compliance.
With the ability to foresee your attackers’ next steps, you no longer need to fear vulnerabilities that could lead to irreparable damage or jeopardize your compliance.
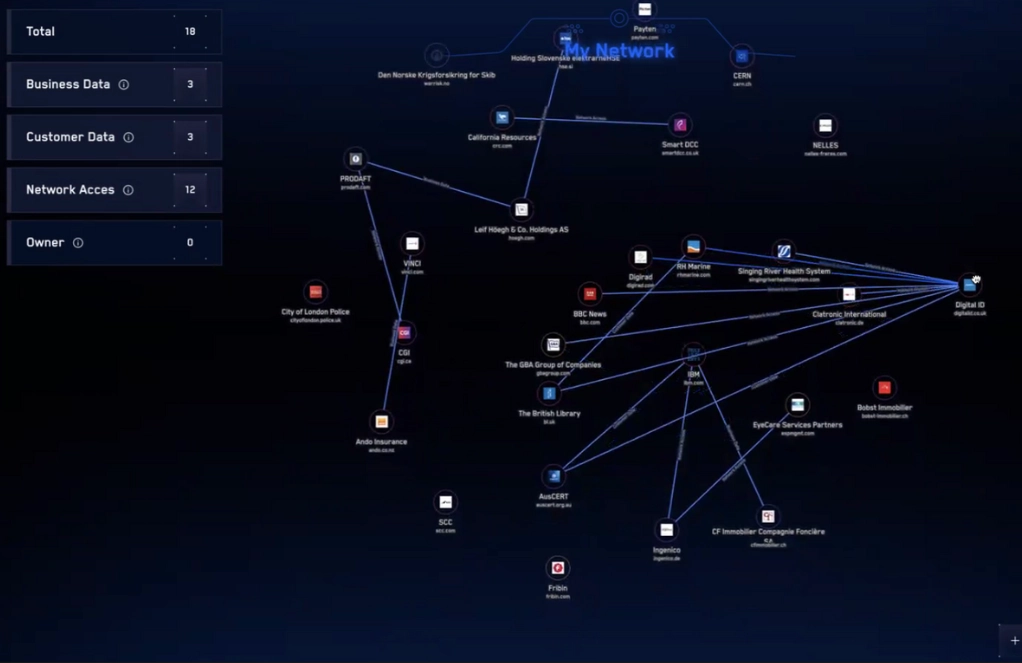
Instead, you gain access to an already established connection graph that maps the risk-laden networks that are truly relevant to your organization.
The underlying intelligence sources can be adapted at any time to your individual priorities and objectives – precisely tailored to your requirements.
Get real intelligence.
Turn complexity into clarity. Act before threats become incidents.


